
HIPAA Compliance Checklist for Audit & Assessment
As a healthcare business, it’s crucial to prioritize HIPAA (Health Insurance Portability and Accountability Act) compliance to protect patient data and avoid potential legal ramifications. With the ever-evolving regulatory landscape, preparing for audits and assessments can be challenging. This article outlines a comprehensive HIPAA compliance checklist to ensure your healthcare organization meets all requirements and maintains patient data security.
HIPAA Compliance Guidelines to Secure Patient Data
In nutshell, HIPAA Compliance Guidelines can be summed up in the following three points:
- Understand HIPAA Privacy, Security, and Breach Notification Rules: To begin, familiarize yourself with the three main HIPAA rules:
- Privacy Rule: Protects individuals’ medical records and personal health information (PHI)
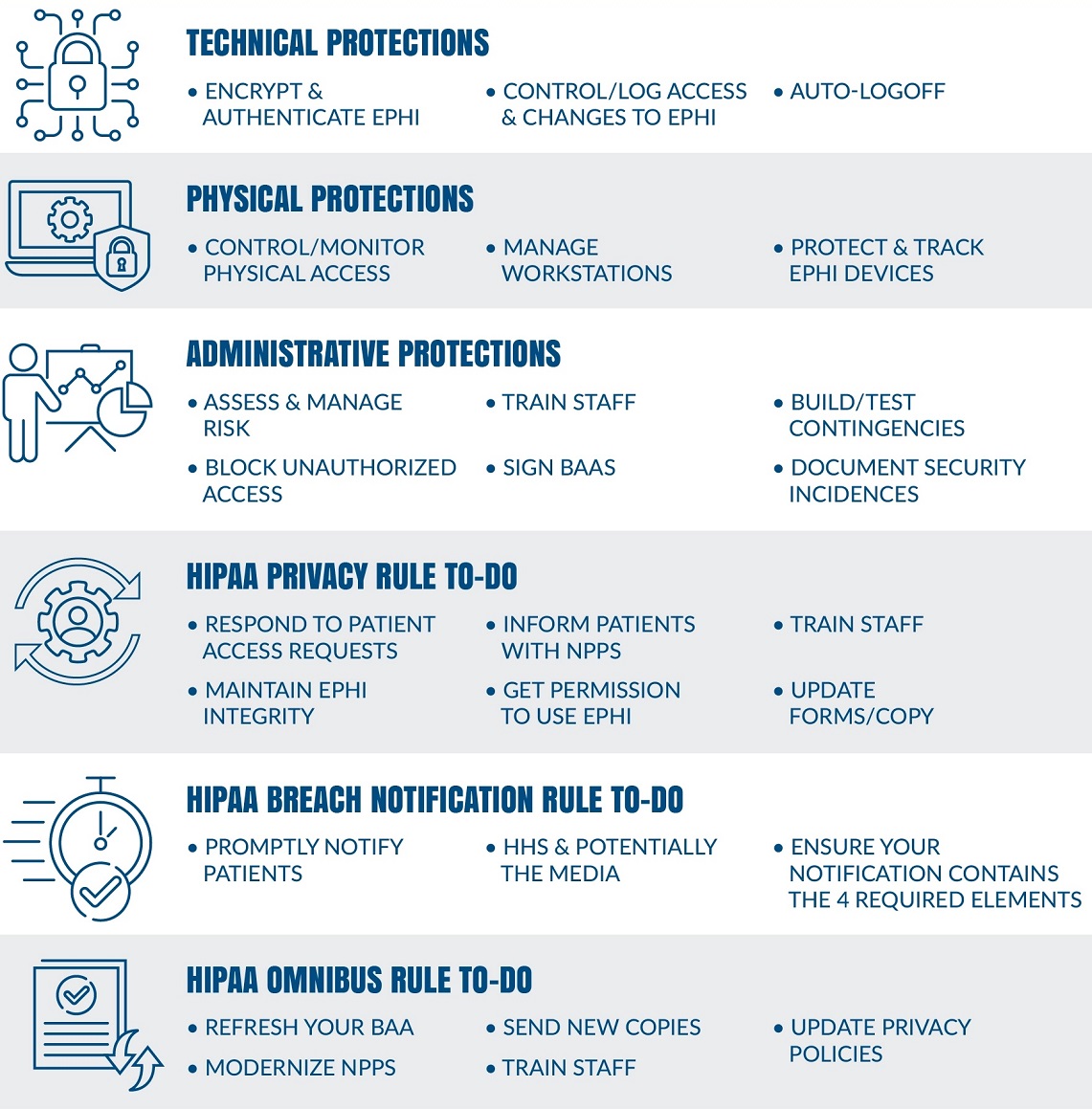
- Security Rule: Outlines the administrative, physical, and technical safeguards for electronic PHI (ePHI)
- Breach Notification Rule: Requires covered entities and business associates to notify affected individuals, the Department of Health and Human Services (HHS), and the media (in certain cases) in the event of a breach involving unsecured PHI
- Assign a HIPAA Privacy and Security Officer: Designate a knowledgeable individual (or individuals) within your organization to oversee HIPAA compliance efforts. This officer will be responsible for developing, implementing, and maintaining your privacy and security policies and procedures.
- Conduct a Thorough Risk Assessment: Perform a risk assessment to identify potential threats and vulnerabilities to PHI in your organization and place people, administrative and technological safeguard to mitigate those risks.
HIPAA Security Rule Checklist
As a healthcare organization, ensuring compliance with the HIPAA Security Rule is critical for protecting patient data and maintaining trust. In this article, we present a comprehensive checklist to help you navigate the complexities of the HIPAA Security Rule and secure electronic Protected Health Information (ePHI). Adhering to this checklist will not only safeguard patient data but also reduce the likelihood of costly penalties and legal repercussions.
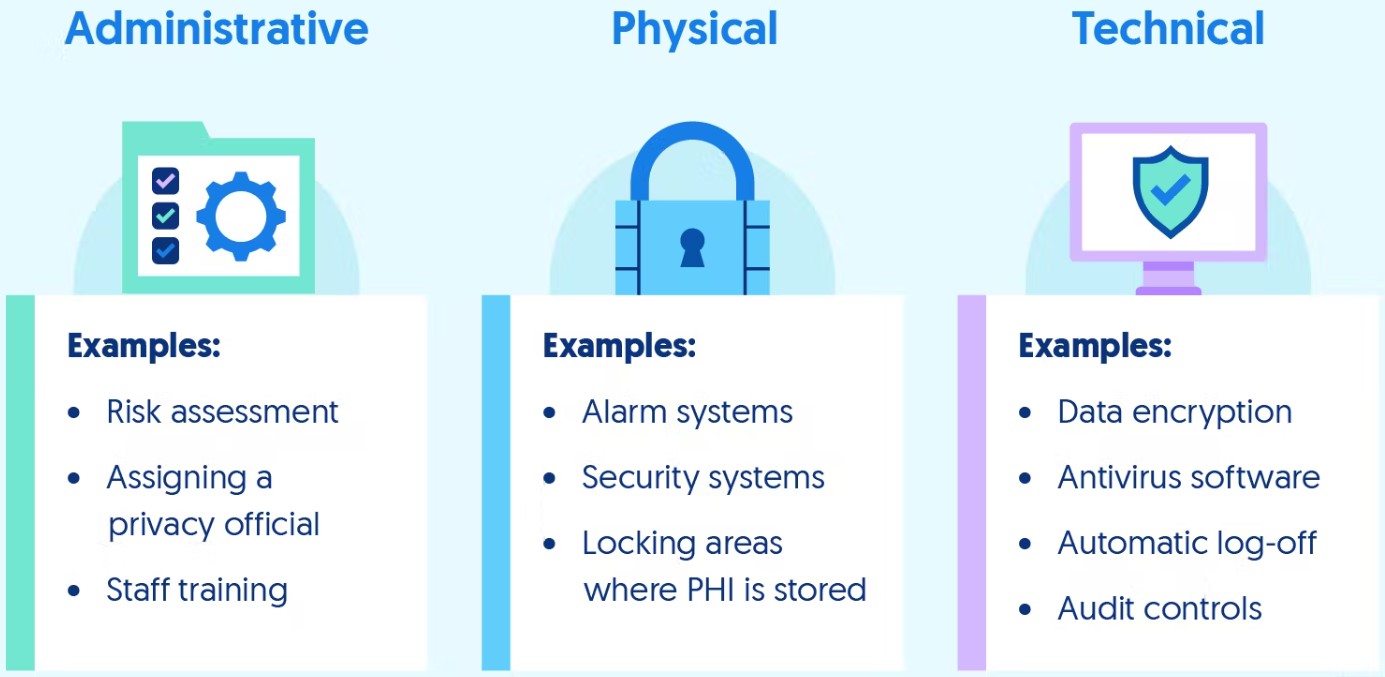
The HIPAA Security Rule outlines administrative, physical, and technical safeguards that organizations must implement to protect ePHI. Familiarize yourself with these requirements to ensure your organization is compliant:
- Administrative Safeguards: Policies and procedures designed to manage and oversee ePHI protection
- Physical Safeguards: Measures to secure the physical access and environment where ePHI is stored, processed, or transmitted
- Technical Safeguards: Technology and methods used to control access and secure ePHI during storage and transmission
HIPAA Privacy Rule Checklist
Compliance with the HIPAA Privacy Rule is essential for safeguarding patient privacy and avoiding potential legal consequences. In this article, we present a comprehensive checklist to help you understand and adhere to the requirements of the HIPAA Privacy Rule, ensuring your organization remains compliant and maintains the trust of your patients.
The HIPAA Privacy Rule sets the standards for the protection of individuals’ medical records and personal health information (PHI). It applies to healthcare providers, health plans, healthcare clearinghouses, and business associates. Understanding the scope and requirements of the Privacy Rule is the first step toward compliance.
Designate a knowledgeable individual within your organization as the HIPAA Privacy Officer. This individual will be responsible for developing, implementing, and maintaining privacy policies and procedures in accordance with the Privacy Rule.
Create privacy policies and procedures that outline how your organization will protect PHI. These documents should address the following:
- Use and disclosure of PHI
- Rights of individuals regarding their PHI
- Minimum necessary standard for accessing and disclosing PHI
- Notice of Privacy Practices
- Privacy training and awareness programs for employees
HIPAA Risk Assessment Checklist
A thorough risk assessment is a crucial aspect of HIPAA compliance. Identifying potential threats and vulnerabilities to protected health information (PHI) helps healthcare organizations establish the necessary safeguards to ensure data security. This article presents a comprehensive HIPAA risk assessment checklist to help your organization maintain compliance and protect patient data.
- Understand the Purpose of a Risk Assessment
A risk assessment is a systematic process that identifies potential threats, vulnerabilities, and the likelihood of a breach involving PHI. It’s essential for:
- Ensuring compliance with the HIPAA Security Rule
- Protecting patient data from unauthorized access, alteration, or destruction
- Establishing a baseline for ongoing risk management
- Assemble a Risk Assessment Team
Form a team that includes representatives from various departments within your organization, such as IT, compliance, and human resources. This multidisciplinary approach ensures a comprehensive assessment of risks to PHI.
- Inventory and Categorize ePHI
Create an inventory of all electronic devices, systems, and applications that store, process, or transmit PHI. Categorize the ePHI based on its sensitivity and the potential impact of a breach.
- Identify and Assess Threats and Vulnerabilities
Examine your organization’s environment and operations to identify potential threats and vulnerabilities to ePHI. Consider both internal and external factors, such as:
- Unauthorized access to systems or devices
- Malware or ransomware attacks
- Insider threats (e.g., employee negligence or malicious behavior)
- Physical theft or loss of devices
- Inadequate backup and disaster recovery processes
- Assess Current Security Measures
Evaluate the administrative, physical, and technical safeguards currently in place to protect ePHI. Determine if these measures are sufficient or if additional safeguards are needed to address identified risks.
- Determine the Likelihood and Impact of Risks
Assess the likelihood of a threat exploiting a vulnerability and the potential impact on your organization. Consider factors such as the probability of occurrence, potential harm to individuals, and financial or reputational consequences.
- Prioritize and Manage Risks
Develop a risk management plan that outlines strategies for mitigating identified risks. Prioritize risks based on their likelihood and impact, and allocate resources accordingly to address them.
- Document Your Risk Assessment Process
Maintain thorough documentation of your risk assessment process, findings, and remediation efforts. This documentation is essential for demonstrating HIPAA compliance during audits or investigations.
- Review and Update Your Risk Assessment Regularly
Risk assessments should be an ongoing process, with periodic reviews and updates to ensure that new risks are identified and addressed. Establish a schedule for conducting risk assessments (e.g., annually) or when significant changes occur within your organization.
By following this HIPAA risk assessment checklist, your healthcare organization can identify and mitigate potential threats to patient data, ensuring compliance with HIPAA regulations and maintaining the trust of your patients.
HIPAA Administrative Safeguards Checklist
Administrative safeguards play a critical role in protecting PHI (Protected Health Information) and maintaining HIPAA compliance. They provide a framework for managing ePHI (electronic Protected Health Information) security and ensuring that your healthcare organization has the necessary policies and procedures in place. This article presents a comprehensive HIPAA Administrative Safeguards checklist to help you establish a solid foundation for data security and compliance.
- Designate a HIPAA Privacy and Security Officer
Assign one or more knowledgeable individuals within your organization to oversee HIPAA compliance efforts. The Privacy and Security Officer(s) will be responsible for developing, implementing, and maintaining privacy and security policies and procedures.
- Develop and Implement Policies and Procedures
Create and implement written policies and procedures that address the following key areas:
- Access to PHI: Define the roles, responsibilities, and levels of access for employees who handle PHI.
- Workforce Training and Management: Develop a training program to ensure all employees understand their responsibilities related to PHI and the HIPAA regulations.
- Incident Response and Reporting: Establish procedures for identifying, reporting, and responding to security incidents or breaches.
- Disciplinary Actions: Outline the consequences for employees who fail to comply with HIPAA regulations or internal policies.
- Conduct Regular Risk Assessments
Perform periodic risk assessments to identify potential threats and vulnerabilities to PHI, and evaluate the effectiveness of your organization’s security measures. Use the findings to update your policies and procedures as needed.
- Establish a Risk Management Plan
Create a risk management plan that outlines the strategies and measures to mitigate identified risks. Prioritize risks based on their likelihood and impact, and allocate resources accordingly.
- Develop a Contingency Plan
Develop and implement a contingency plan to address emergencies or disasters that could compromise PHI. This plan should include:
- Data backup procedures
- Disaster recovery processes
- Emergency mode operation plans
- Testing and revision of contingency plans
- Implement Workforce Clearance and Termination Procedures
Establish procedures to determine if employees have the appropriate level of access to PHI and the necessary background checks. Develop termination procedures to ensure prompt removal of access to PHI when employees leave the organization.
- Implement a Business Associate Management Process
Develop a process for managing relationships with business associates who handle PHI on your organization’s behalf. This includes:
- Identifying and documenting business associates
- Ensuring that appropriate Business Associate Agreements (BAAs) are in place
- Monitoring business associates’ compliance with HIPAA regulations
- Review and Update Policies and Procedures Regularly
Regularly review and update your administrative policies and procedures to ensure they remain current and effective. This process should be conducted at least annually or whenever significant changes occur within your organization.
HIPAA Technical Safeguards Checklist
Technical safeguards are essential for healthcare organizations to ensure the security of electronic protected health information (ePHI). These measures help control access, protect data integrity, and maintain HIPAA compliance. This article presents a comprehensive HIPAA Technical Safeguards checklist to help you implement the necessary measures to protect your patients’ sensitive data.
- Access Control
Implement access control measures to ensure that only authorized personnel can access ePHI. These measures should include:
- Unique User Identification: Assign a unique username or number to each employee to track their access and activity related to ePHI.
- Emergency Access Procedure: Establish procedures for granting access to ePHI during emergencies.
- Automatic Logoff: Implement systems that automatically log users off after a predetermined period of inactivity to prevent unauthorized access.
- Encryption and Decryption: Encrypt ePHI during storage and transmission to protect it from unauthorized access.
- Audit Controls
Implement audit controls to record and examine activity within systems that contain or use ePHI. These controls should:
- Capture information about user actions, access, and modifications to ePHI.
- Regularly review audit logs and reports to identify suspicious or unauthorized activities.
- Implement a process for responding to potential security incidents detected through audit controls.
- Integrity Controls
Establish measures to ensure the integrity of ePHI, preventing unauthorized alteration or destruction. These controls should include:
- Mechanisms to authenticate ePHI: Implement methods to verify that ePHI has not been altered or destroyed in an unauthorized manner, such as checksums or digital signatures.
- Mechanisms to corroborate ePHI source: Employ methods to confirm the authenticity of ePHI and its source.
- Authentication Controls
Implement procedures to verify that a person or entity seeking access to ePHI is who they claim to be. Authentication methods may include:
- Passwords or personal identification numbers (PINs)
- Two-factor authentication (e.g., using a token or biometric data in addition to a password)
- Digital certificates and public key infrastructure (PKI)
- Transmission Security
Transmission security is necessary to ensure that ePHI is protected during transmission over an electronic network. This includes:
- Implementing measures to encrypt ePHI during transmission over an electronic network
- Implementing procedures to ensure that ePHI is not intercepted during transmission
Protect ePHI during electronic transmission by implementing transmission security measures, such as:
- Integrity Controls: Use methods to ensure that ePHI has not been tampered with during transmission, such as checksums or digital signatures.
- Encryption: Encrypt ePHI during transmission to protect it from unauthorized access or interception.
HIPAA Physical Safeguards Checklist
By following this HIPAA physical safeguards checklist, you can ensure that your organization is in compliance with HIPAA regulations and is protecting individuals’ ePHI.
- Facility Access Controls
Facility access controls are necessary to prevent unauthorized access to areas where ePHI is stored. This includes:
- Implementing a security system that controls access to the facility
- Ensuring that access controls are in place for doors, windows, and other entry points
- Implementing a visitor sign-in process to monitor who enters the facility
- Restricting access to areas where ePHI is stored to authorized personnel only
- Workstation Security
Workstation security is necessary to prevent unauthorized access to ePHI on computers and other electronic devices. This includes:
- Implementing password-protected login screens for all workstations
- Ensuring that workstations are located in secure areas that are only accessible to authorized personnel
- Logging off or locking workstations when they are not in use
- Ensuring that all electronic devices that contain ePHI are encrypted to protect against unauthorized access
- Device and Media Controls
Device and media controls are necessary to prevent unauthorized access to ePHI stored on portable electronic devices or removable media. This includes:
- Implementing policies and procedures for the use and disposal of portable electronic devices and removable media
- Ensuring that all portable electronic devices and removable media are encrypted to protect against unauthorized access
- Implementing physical safeguards to protect against theft or loss of portable electronic devices and removable media
- Ensuring that all ePHI stored on portable electronic devices or removable media is erased or destroyed before disposal
- Data Backup and Storage
Data backup and storage are necessary to ensure the availability of ePHI in the event of a disaster or system failure. This includes:
- Implementing a data backup plan to ensure that ePHI is backed up regularly
- Ensuring that data backups are stored in a secure location that is only accessible to authorized personnel
- Implementing procedures to ensure the integrity and reliability of data backups
- Implementing a disaster recovery plan to ensure that ePHI is available in the event of a disaster or system failure
HIPAA Training Checklist
HIPAA training checklist should cover all the necessary components for a successful HIPAA compliance program:
- Develop a Training Program
The first step in implementing a successful HIPAA training program is to develop a training plan. This plan should include:
- A list of all employees who require training.
- A timeline for when training will be completed.
- A description of the topics that will be covered in the training program.
- Identify HIPAA Requirements
The next step in the HIPAA training checklist is to identify the specific HIPAA requirements that your employees need to be trained on. Some of the key HIPAA requirements include:
- The Privacy Rule
- The Security Rule
- The Breach Notification Rule
- The Omnibus Rule
- Designate a HIPAA Officer
To ensure that your HIPAA compliance program is effective, it is essential to designate a HIPAA officer. This person should be responsible for overseeing the training program and ensuring that all employees are compliant with HIPAA regulations.
- HIPAA Training Plan for Staff
Once you have developed a training plan and identified the specific HIPAA requirements, it is time to provide training to your employees. The training should cover the following topics:
- The importance of HIPAA compliance
- The specific HIPAA regulations that apply to your organization
- The consequences of non-compliance
- How to report HIPAA violations
- Monitor Compliance
After the training program is completed, it is important to monitor compliance to ensure that all employees are following HIPAA regulations. This can be done through regular audits and by providing ongoing education and training.
HIPAA compliance training is essential for all healthcare providers to ensure that patient data is protected. By following this HIPAA training checklist, you can develop a successful HIPAA compliance program that will keep your organization compliant with HIPAA regulations.
HIPAA Compliance Audit Checklist
In the end, let’s recap by following a HIPAA compliance audit checklist, to ensure that your organization is prepared for a HIPAA compliance audit and avoid costly fines and penalties.
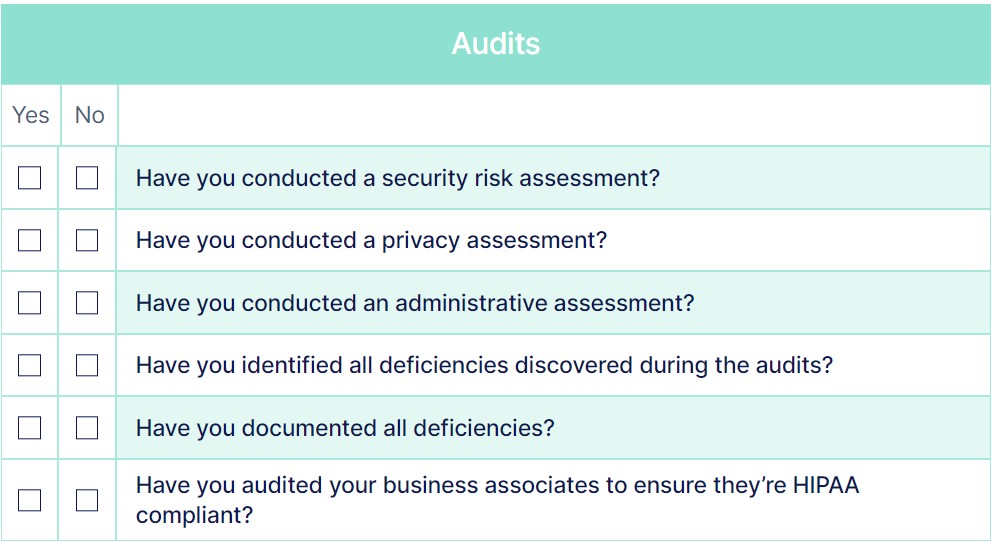
- Risk Analysis
The first step in preparing for a HIPAA compliance audit is to conduct a risk analysis. This analysis will identify potential risks to the confidentiality, integrity, and availability of electronic protected health information (ePHI). A risk analysis should include:
- Identification of all ePHI that your organization creates, receives, maintains, or transmits
- Evaluation of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI
- Documentation of the security measures that your organization has implemented to address the identified risks and vulnerabilities
- Policies and Procedures
The next step in the HIPAA compliance audit checklist is to develop policies and procedures that address HIPAA regulations. This should include policies and procedures for:
- Physical security
- Administrative security
- Technical security
- Incident response
- Business associate agreements
- Staff Training
All employees who handle ePHI must receive HIPAA training. This training should include:
- HIPAA privacy and security regulations
- The organization’s policies and procedures related to HIPAA compliance
- The consequences of violating HIPAA regulations
- Technical Safeguards
Technical safeguards are necessary to protect ePHI. These safeguards include:
- Access control
- Audit controls
- Integrity controls
- Transmission security
- Monitoring
HIPAA compliance is an ongoing process. It is important to perform ongoing monitoring to ensure that your organization remains in compliance with HIPAA regulations. This should include:
- Regular audits of policies and procedures
- Review of security measures
- Analysis of security incidents
- Documentation of compliance activities
HIPAA compliance audit is an essential part of ensuring that healthcare organizations are protecting individuals’ medical records and personal health information. By following this HIPAA compliance audit checklist, you can prepare for an audit and ensure that your organization is compliant with HIPAA regulations.
Remember, HIPAA compliance is an ongoing process that requires continuous monitoring, education, and training. If you need assistance in preparing for a HIPAA compliance audit or developing a HIPAA compliance program, contact us today. Our team of HIPAA compliance experts can help you develop a customized program that meets the specific needs of your organization.




